- What Does Mac In Mac Address Stand For
- What Does Bia Stand For Mac Address
- What Does Mac Address Stand For
- What Does Mac Address Stand For In Computers
- What Does Mac Address Stand For
- What Does Mac Stand For In A Mailing Address
Discover which company built a networked interface by MAC Address.
- IP Address Relationship. TCP/IP networks use both MAC addresses and IP addresses, but for separate purposes. A MAC address remains fixed to the device's hardware, while the IP address for that same device can be changed depending on its TCP/IP network configuration.
- Since ethernet uses MAC addresses, the sender needs to get the MAC address of the next hop. There is a special protocol ARP (address resolution protocol) that is used for that. Once the sender has retrieved the MAC address of the next hop, he writes that target MAC address into the packet and sends the packet.
MAC ID (Media Access Control) is a unique digital number assigned to each computer on the network, more precisely not to a computer, but to a network card. The MAC address is registered on the network card when it is created in the factory.
- Several formats accepted:
00-1C-23-59-5A-92,001c23595a92,00:1C:23:59:5A:92 - Partial searches are accepted:
001c,2359:92 - Uses several databases including NMAP, IEEE Official List, Wireshark Info, and more.
- Never know what else may show up ;)
MAC address
A media access control address (MAC address) is a unique identifier assigned to network interfaces for communications on the physical network segment. MAC addresses are used as a network address for most IEEE 802 network technologies, including Ethernet. Logically, MAC addresses are used in the media access control protocol sublayer of the OSI reference model.
MAC addresses are most often assigned by the manufacturer of a network interface controller (NIC) and are stored in its hardware, such as the card's read-only memory or some other firmware mechanism. If assigned by the manufacturer, a MAC address usually encodes the manufacturer's registered identification number and may be referred to as the burned-in address (BIA). It may also be known as an Ethernet hardware address (EHA), hardware address or physical address. This can be contrasted to a programmed address, where the host device issues commands to the NIC to use an arbitrary address.
A network node may have multiple NICs and each must have one unique MAC address per NIC.
MAC addresses are formed according to the rules of one of three numbering name spaces managed by the Institute of Electrical and Electronics Engineers (IEEE): MAC-48, EUI-48, and EUI-64. The IEEE claims trademarks on the names EUI-48 and EUI-64, in which EUI is an abbreviation for Extended Unique Identifier.
Notational conventions
The standard (IEEE 802) format for printing MAC-48 addresses in human-friendly form is six groups of two hexadecimal digits, separated by hyphens (-) or colons (:), in transmission order (e.g. 01-23-45-67-89-ab or 01:23:45:67:89:ab ). This form is also commonly used for EUI-64. Another convention used by networking equipment uses three groups of four hexadecimal digits separated by dots (.) (e.g. 0123.4567.89ab ), again in transmission order.
Address details
The original IEEE 802 MAC address comes from the original Xerox Ethernet addressing scheme. This 48-bit address space contains potentially 248 or 281,474,976,710,656 possible MAC addresses.
All three numbering systems use the same format and differ only in the length of the identifier. Addresses can either be universally administered addresses or locally administered addresses. A universally administered address is uniquely assigned to a device by its manufacturer. The first three octets (in transmission order) identify the organization that issued the identifier and are known as the Organizationally Unique Identifier (OUI). The following three (MAC-48 and EUI-48) or five (EUI-64) octets are assigned by that organization in nearly any manner they please, subject to the constraint of uniqueness. The IEEE has a target lifetime of 100 years for applications using MAC-48 space, but encourages adoption of EUI-64s instead. A locally administered address is assigned to a device by a network administrator, overriding the burned-in address. Locally administered addresses do not contain OUIs.
Universally administered and locally administered addresses are distinguished by setting the second-least-significant bit of the most significant byte of the address. This bit is also referred to as the U/L bit, short for Universal/Local, which identifies how the address is administered. If the bit is 0, the address is universally administered. If it is 1, the address is locally administered. In the example address 06-00-00-00-00-00 the most significant byte is 06 (hex), the binary form of which is 00000110, where the second-least-significant bit is 1. Therefore, it is a locally administered address. Consequently, this bit is 0 in all OUIs.
If the least significant bit of the most significant octet of an address is set to 0 (zero), the frame is meant to reach only one receiving NIC. This type of transmission is called unicast. A unicast frame is transmitted to all nodes within the collision domain, which typically ends at the nearest network switch or router. A switch will forward a unicast frame through all of its ports (except for the port that originated the frame) if the switch has no knowledge of which port leads to that MAC address, or just to the proper port if it does have knowledge. Only the node with the matching hardware MAC address will accept the frame; network frames with non-matching MAC-addresses are ignored, unless the device is in promiscuous mode.
If the least significant bit of the most significant address octet is set to 1, the frame will still be sent only once; however, NICs will choose to accept it based on criteria other than the matching of a MAC address: for example, based on a configurable list of accepted multicast MAC addresses. This is called multicast addressing.
The following technologies use the MAC-48 identifier format:
- Ethernet
- 802.11 wireless networks
- IEEE 802.5 token ring
- most other IEEE 802 networks
- Fiber Distributed Data Interface (FDDI)
- Asynchronous Transfer Mode (ATM), switched virtual connections only, as part of an NSAP address
- Fibre Channel and Serial Attached SCSI (as part of a World Wide Name)
- The ITU-TG.hn standard, which provides a way to create a high-speed (up to 1 gigabit/s) local area network using existing home wiring (power lines, phone lines and coaxial cables). The G.hn Application Protocol Convergence (APC) layer accepts Ethernet frames that use the MAC-48 format and encapsulates them into G.hn Medium Access Control Service Data Units (MSDUs).
Every device that connects to an IEEE 802 network (such as Ethernet and WiFi) has a MAC-48 address. Common consumer devices to use MAC-48 include every PC, iPhone, iPad, and Android-based devices.
The distinction between EUI-48 and MAC-48 identifiers is purely nominal: MAC-48 is used for network hardware; EUI-48 is used to identify other devices and software. (Thus, by definition, an EUI-48 is not in fact a 'MAC address', although it is syntactically indistinguishable from one and assigned from the same numbering space.)
The IEEE now considers the label MAC-48 to be an obsolete term, previously used to refer to a specific type of EUI-48 identifier used to address hardware interfaces within existing 802-based networking applications, and thus not to be used in the future. Instead, the proprietary term EUI-48 should be used for this purpose.
The EUI-48 is expected to have its address space exhausted by the year 2100.
EUI-64 identifiers are used in:
- IPv6 (Modified EUI-64 as the least-significant 64 bits of a unicast network address or link-local address when stateless autoconfiguration is used)
- ZigBee / 802.15.4 / 6LoWPAN wireless personal-area networks
The IEEE has built in several special address types to allow more than one network interface card to be addressed at one time:
- Packets sent to the broadcast address, all one bits, are received by all stations on a local area network. In hexadecimal the broadcast address would be
FF:FF:FF:FF:FF:FF. A broadcast frame is flooded and is forwarded to and accepted by all other nodes. - Packets sent to a multicast address are received by all stations on a LAN that have been configured to receive packets sent to that address.
- Functional addresses identify one or more Token Ring NICs that provide a particular service, defined in IEEE 802.5.
These are all examples of group addresses, as opposed to individual addresses; the least significant bit of the first octet of a MAC address distinguishes individual addresses from group addresses. That bit is set to 0 in individual addresses and set to 1 in group addresses. Group addresses, like individual addresses, can be universally administered or locally administered.
In addition, the EUI-64 numbering system encompasses both MAC-48 and EUI-48 identifiers by a simple translation mechanism. To convert a MAC-48 into an EUI-64, copy the OUI, append the two octets FF-FF and then copy the organization-specified extension identifier. To convert an EUI-48 into an EUI-64, the same process is used, but the sequence inserted is FF-FE. In both cases, the process can be trivially reversed when necessary. Organizations issuing EUI-64s are cautioned against issuing identifiers that could be confused with these forms. The IEEE policy is to discourage new uses of 48-bit identifiers in favor of the EUI-64 system.
IPv6 — one of the most prominent standards that uses a Modified EUI-64 — treats MAC-48 as EUI-48 instead (as it is chosen from the same address pool) and toggles the U/L bit (as this makes it easier to type locally assigned IPv6 addresses based on the Modified EUI-64). This results in extending MAC addresses (such as IEEE 802 MAC address) to Modified EUI-64 using only FF-FE (and never FF-FF) and with the U/L bit inverted.
Individual address block
An Individual Address Block is a 24-bit OUI managed by the IEEE Registration Authority, followed by 12 IEEE-provided bits (identifying the organization), and 12 bits for the owner to assign to individual devices. An IAB is ideal for organizations requiring fewer than 4097 unique 48-bit numbers (EUI-48).
Mac Address Usage in hosts
Although intended to be a permanent and globally unique identification, it is possible to change the MAC address on most modern hardware. Changing MAC addresses is necessary in network virtualization. It can also be used in the process of exploiting security vulnerabilities. This is called MAC spoofing.
A host cannot determine from the MAC address of another host whether that host is on the same link (network segment) as the sending host, or on a network segment bridged to that network segment.
In IP networks, the MAC address of an interface can be queried given the IP address using the Address Resolution Protocol (ARP) for Internet Protocol Version 4 (IPv4) or the Neighbor Discovery Protocol (NDP) for IPv6. In this way, ARP or NDP is used to translate IP addresses (OSI layer 3) into Ethernet MAC addresses (OSI layer 2). On broadcast networks, such as Ethernet, the MAC address uniquely identifies each node on that segment and allows frames to be marked for specific hosts. It thus forms the basis of most of the link layer (OSI Layer 2) networking upon which upper layer protocols rely to produce complex, functioning networks.
Mac Address Usage in switches
What Does Mac In Mac Address Stand For
Layer 2 switches use MAC addresses to restrict packet transmission to the intended recipient. However, the effect is not immediate.
Bit-reversed notation
The standard notation, also called canonical format, for MAC addresses is written in transmission bit order with the least significant bit transmitted first, as seen in the output of the iproute2/ifconfig/ipconfig command, for example.
However, since IEEE 802.3 (Ethernet) and IEEE 802.4 (Token Bus) send the bytes (octets) over the wire, left-to-right, with least significant bit in each byte first, while IEEE 802.5 (Token Ring) and IEEE 802.6 send the bytes over the wire with the most significant bit first, confusion may arise when an address in the latter scenario is represented with bits reversed from the canonical representation. For example, an address in canonical form 12-34-56-78-9A-BC would be transmitted over the wire as bits 01001000 00101100 01101010 00011110 01011001 00111101 in the standard transmission order (least significant bit first). But for Token Ring networks, it would be transmitted as bits 00010010 00110100 01010110 01111000 10011010 10111100 in most-significant-bit first order. The latter might be incorrectly displayed as 48-2C-6A-1E-59-3D. This is referred to as bit-reversed order, non-canonical form, MSB format, IBM format, or Token Ring format, as explained in RFC 2469. Canonical form is generally preferred, and used by all modern implementations.
When the first switches supporting both Token Ring and Ethernet came out, some did not distinguish between canonical form and non-canonical form and so did not reverse MAC address bits as required. This led to cases of duplicate MAC addresses in the field.
See also

- Hot Standby Router Protocol or standard alternative VRRP Virtual Router Redundancy Protocol, which allows multiple routers to share one IP address and MAC address to provide router redundancy. The OpenBSD project has an open source alternative, the Common Address Redundancy Protocol (CARP). On Linux, iptables has a CLUSTERIP target.
- NSAP address, another endpoint addressing scheme.
- Sleep Proxy Service, which may 'take over' another device's MAC address during certain periods
References
- IEEE Std 802-2001. The Institute of Electrical and Electronics Engineers, Inc. (IEEE). 2002-02-07. p. 19. 'The universal administration of LAN MAC addresses began with the Xerox Corporation administering Block Identifiers (Block IDs) for Ethernet addresses.'
- 'Guidelines for use of the 24-bit Organizationally Unique Identifiers (OUI)'. IEEE-SA.
- 'Standard Group MAC Addresses: A Tutorial Guide'. IEEE-SA.
- 'Guidelines for Fibre Channel Use of the Organizationally Unique Identifier (OUI)'. IEEE-SA.
- 'Network Interface Controller'. Wikipedia.
- 'Guidelines for 64-bit Global Identifier (EUI-64)'. IEEE-SA.
- RFC 5342'IANA Considerations and IETF Protocol Usage for IEEE 802 Parameters'. IETF. September 2008.
- IEEE-RA. 'What is an Individual Address Block?'.
External links
- Wireshark's OUI Lookup Tool and MAC address list
Each network-compatible device has at least one unique hardware ID – the media access control address (in short: MAC address). What this is all about and how you can find or rewrite the MAC address is explained below.
- What is a MAC address?
- Finding out your MAC address: a how-to guide
- Assigning the MAC address using software
What is a MAC address?
Each device that is integrated into a computer network requires a network adaptor. This adapter receives a worldwide unique identification number from the manufacturer: the MAC address. This enables devices like desktop computers, tablets, or mobile phones to be identified in the network and addressed as required. If a device has several network adapters (for example, for several LAN connections or different communication standards like Ethernet, WiFi, FDDI, Bluetooth, or Token Ring), a different address is available for each standard.
The MAC address (short for media access control address) is the worldwide unique hardware address of a single network adapter. The physical address is used to identify a device in computer networks.
Since MAC addresses are assigned directly by the hardware manufacturer, they are also referred to as hardware addresses. With Microsoft Windows, the MAC address is referred to as the physical address. Apple uses the terms Ethernet ID, Airport ID, or WiFi address, depending on the communication standard. The term device address, on the other hand, is fuzzy, since a device can have several network adapters and therefore different MAC addresses.
The MAC address in practice
Conflicting MAC addresses are a basic requirement for error-free network communication.
Data transmission in computer networks is a complex communication process in which different requirements including reliability, security, and efficiency must be met. This can be illustrated using the OSI models (abbreviation for open systems interconnection) – a reference model developed by the ISO (International Organization for Standardization) that maps network communication to 7 layers. During data transmission, each layer of the OSI model is run through on both the sender and receiver sides.
MAC addresses are used on the backup layer (layer 2) of the OSI model – actually, the media access controlsublayer introduced by the Institute of Electrical and Electronics Engineers (IEEE).
In the extension of the OSI model designed by the IEEE, the backup layer (layer 2) is divided into the sublayers media access control (2a) and logical link control (2b).
The backup layer is located between the bit transfer layer (layer 1) and the switching layer (layer 3). While the bit transmission layer provides protocols and tools responsible for maintaining the physical connection, protocols on the backup layer control how different systems share the available transmission medium. Secure system connections are abstracted from the physical connection. The actual transmission of data packets takes place at the switching level via IP.
What Does Bia Stand For Mac Address

For example, if you want to send an IP packet over Ethernet, your computer transmits a data frame that is addressed to the target computer’s MAC address on the backup layer, according to the OSI model.
What Does Mac Address Stand For
If the target computer is not in the local network, a router is addressed and instructed to forward it to the internet. Routers integrated into a social network also have a unique MAC address.
An Ethernet data frame contains information that is read out at different levels of the OSI model.
Data frames in IPv4 networks contain the following components:
- Destination address (destination computer MAC address)
- Source address (sender’s MAC address)
- Control information for data flow control
- User data (the data packet that needs to be transmitted later on the switching layer)
- Checksums that ensure data integrity
A target computer that receives a data frame first reads it on the backup layer and compares the target address of the frame with its own MAC address. If the addresses match, the target computer starts interpreting the frame at the next higher level.
Network devices that are only used to forward data packets (repeaters) or manage parts of the network (bridges and switches) usually do not actively participate in network communication and so do not require their own MAC addresses.
To link the address assignment on the backup layer with the address assignment on the switching layer, the address resolution protocol (ARP) is used in IPv4 networks. Each computer in the local network maintains an ARP table whereby IP addresses are assigned to MAC addresses.
ARP is vulnerable to an attack pattern called ARP spoofing. The danger of ARP spoofing and the countermeasures you can take are discussed in the article above.
The new internet protocol standard IPv6 uses the neighbor discovery protocol (NDP).
MAC address syntax
MAC addresses in LAN or WLAN networks consist of 6 bytes (48 bits) and are written in hexadecimal notation. The use of separators such as hyphens or colons between two bytes increases readability.
The following example shows the MAC address of a desktop computer in binary and hexadecimal format:
In our example, we use canonical representation of the bit sequence. This corresponds to the order in which MAC addresses are transmitted in Ethernet. Other communication standards like Token Ring provide for bit-reversed transmission, starting with the most significant bit.
The bit sequence of each MAC address is divided into 4 areas, each of which encodes different information.
- Bit 1 (receiver): The first bit of the MAC address specifies whether it is an individual or group address. This bit is called I/G (short for individual/group). If I/G = 0, it is a unicast address for a single network adapter. Multicast addresses are identified by I/G = 1 and are addressed to several receivers.
- Bit 2 (registry): The second bit of the MAC address indicates whether it is an address with global validity (universal) or whether the address has been assigned locally (local). The bit is called U/L. If U/L = 0, the address is valid worldwide as a universally administered address (UAA). Addresses that are only locally unique are called locally administered address (LAA) and are marked with U/L = 1.
- Bit 3–24 (manufacturer identification): Bits 3 to 24 encode an identifier (organizationally unique identifier, OUI), which is assigned exclusively to hardware manufacturers by IEEE. The assignment of OUIs is usually public and can be determined via databases. A corresponding service is available, for example, on aruljohn.com.
- Bit 25-48 (network adapter identifier): Bits 25 to 48 provide device manufacturers with 24 bits for assigning a unique hardware identifier (organizationally unique address, OUA). This means that 224 (= 16.777.216) unique OUAs can be assigned per OUI.
Table: Subareas of an MAC address
Label | I/G | U/L | OUI | OUA |
Bit | 1. | 2. | 3.–24. | 25.–48. |
Function | Recipient group | Awarding office | Manufacturer code | Network adapter identification |
Finding out your MAC address: a how-to guide
What Does Mac Address Stand For In Computers
MAC addresses can be queried through the terminal in all modern operating systems with little effort – both on the local system and remotely in the network. The following table shows the corresponding command line commands for the most common operating systems.
Table: MAC address read out
| Operating system | Terminal command | Remote |
|---|---|---|
| FreeBSD | ifconfig | arp -a |
| NetBSD | ifconfig -a | arp -a |
| OpenBSD | ifconfig -a | arp -a |
| Linux | ip link | ip neigh |
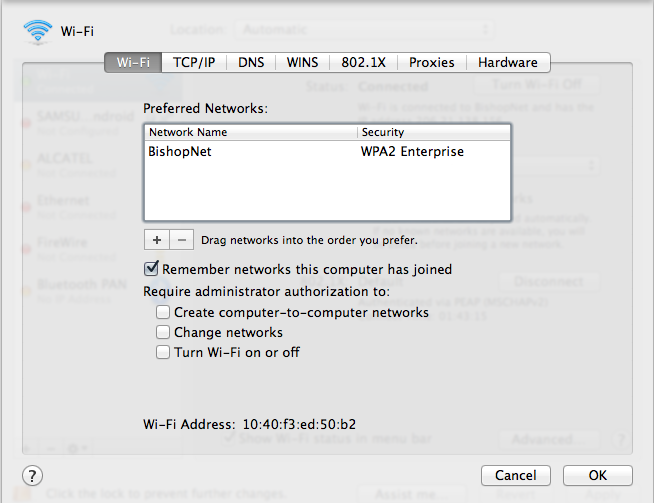
| Mac OS X / macOS | ifconfig | arp -a |
| Solaris | ifconfig -a | arp -a |
| Windows XP Professional | getmac /v | arp -a |
| Windows (ab 2000) | ipconfig /all | arp -a |
On mobile devices, you can display the MAC address in the settings.
Table: Get MAC addresses on mobile devices
| Operating system | Local |
|---|---|
| Android | Settings > Phone Information > Hardware Information |
| Apple iOS | Settings > General > Info > WiFi address |
| Windows Phone 7 | Settings > Info > More Information |
Read MAC address locally
If you want to read out the MAC addresses of the LAN and WiFi adapters on your Windows computer, proceed as follows if using Windows 10.
Step 1: Open the terminal of your operating system. For example, use the keyboard shortcuts [Windows button]+[R]. Then enter “cmd” in the window “Run” and confirm with “OK.”
Step 2: From Windows 2000 onwards you can use the command line utility ipconfig with the “/all” option to get the MAC address of all network adapters on your Windows computer.
Alternatively get the MAC address with the command “getmac /v”
Step 3: With Windows, the MAC address is displayed under “physical address.”
Accessing your MAC address remotely
Thanks to ARP, in IPv4 networks it is possible to determine other devices’ MAC addresses in the same local network. With Windows and most unixoid operating systems, use the command line “arp” with the option to display you system’s ARP table in the terminal.
You will receive a terminal output according to the following scheme:
If you just want to read the MAC address of a specific network adapter remotely, use the command “arp –a” in a combination with the target adapter’s local IPv4 address.
Assigning the MAC address using software
MAC addresses are invariably assigned by device manufacturers and are “burned” into the network adapter chip on the hardware side. However, numerous operating systems offer the option to overwrite hardware addresses on the software side. This is referred to as spoofing. In this case, a system does not send the addressed adapter’s real network hardware address in network communication, but instead a user-defined MAC address.
Assigning an MAC address in Windows
With Windows, you can overwrite the MAC address through the device manager if the network adapter’s device driver supports this function.
Step 1: Open the network adapter settings. To do this, follow the click path: Start à Settings à Network and Internet à Ethernet à Change Adapter Options
Step 2: Right-click on the desired network adapter and select “Disable” in the context menu.
Step 3: Right-click on the desired network adapter and select “Properties” from the context menu. A pop-up window opens called “Network adapter properties.”
Step 4: Click on the “Configure” button in the pop-up window and select the “Locally Administered Address” property under “Advanced.” Enter your chosen software MAC address under “Value.”
Assign MAC address in unixoid operating systems
Unix derivatives such as Linux, macOS, Solaris, and the BSD operating systems support the assignment of MAC addresses through the terminal on the software side.
Table: Overwriting a MAC address
Operating system | Terminal command |
Linux | ip link set dev <Interface> addr XX:XX:XX:XX:XX:XX or ifconfig <Interface> promisc and finally ifconfig <Interface> hw ether XX:XX:XX:XX:XX:XX |
Mac OS X / macOS | ifconfig <Interface> ether XX:XX:XX:XX:XX:XX |
Solaris | ifconfig <Interface> ether XX:XX:XX:XX:XX:XX |
FreeBSD | ifconfig <Interface> link XX:XX:XX:XX:XX:XX |
NetBSD | ifconfig <Interface> link XX:XX:XX:XX:XX:XX activate |
OpenBSD | ifconfig <Interface> lladdr XX:XX:XX:XX:XX:XX |
We illustrate the procedure using the most commonly used Unix derivative: Linux. If you want to change your network adapter’s MAC address, proceed as follows.
Step 1: Open the operating system terminal – for example, with the key combination [CTRL]+[ALT]+[T].

What Does Mac Address Stand For
Step 2: Determine the name and current MAC address of the desired network adapter. To do this, enter the following command in the command line:
Note the hardware address assigned by the manufacturer in case you want to undo the change.
Step 3: Turn off the network adapter by entering the following command in the command line:
Enter the name of the network adapter determined through “ip link” for <Interface>.
Step 4: Overwrite the network address assigned by the manufacturer with one of the options specified in the table.
Enter the chosen MAC address instead of XX:XX:XX:XX:XX:XX
Step 5: Restart the network adapter. Use the following command line command:
To ensure that the selected network adapter is accessible at the MAC address you selected, re-read the network information with “ip link” (see step 1).